How to install Zenmap
How to install Zenmap Zenmap is the official graphical user interface (GUI) for Nmap, a widely used network scanning and security auditing tool. It simplifies Nmap’s functionalities, making them more accessible, especially for users who prefer a visual interface over command-line operations. Why Use Zenmap? User-Friendly Interface: Zenmap provides an intuitive GUI, allowing users to perform complex network scans without …
Read More
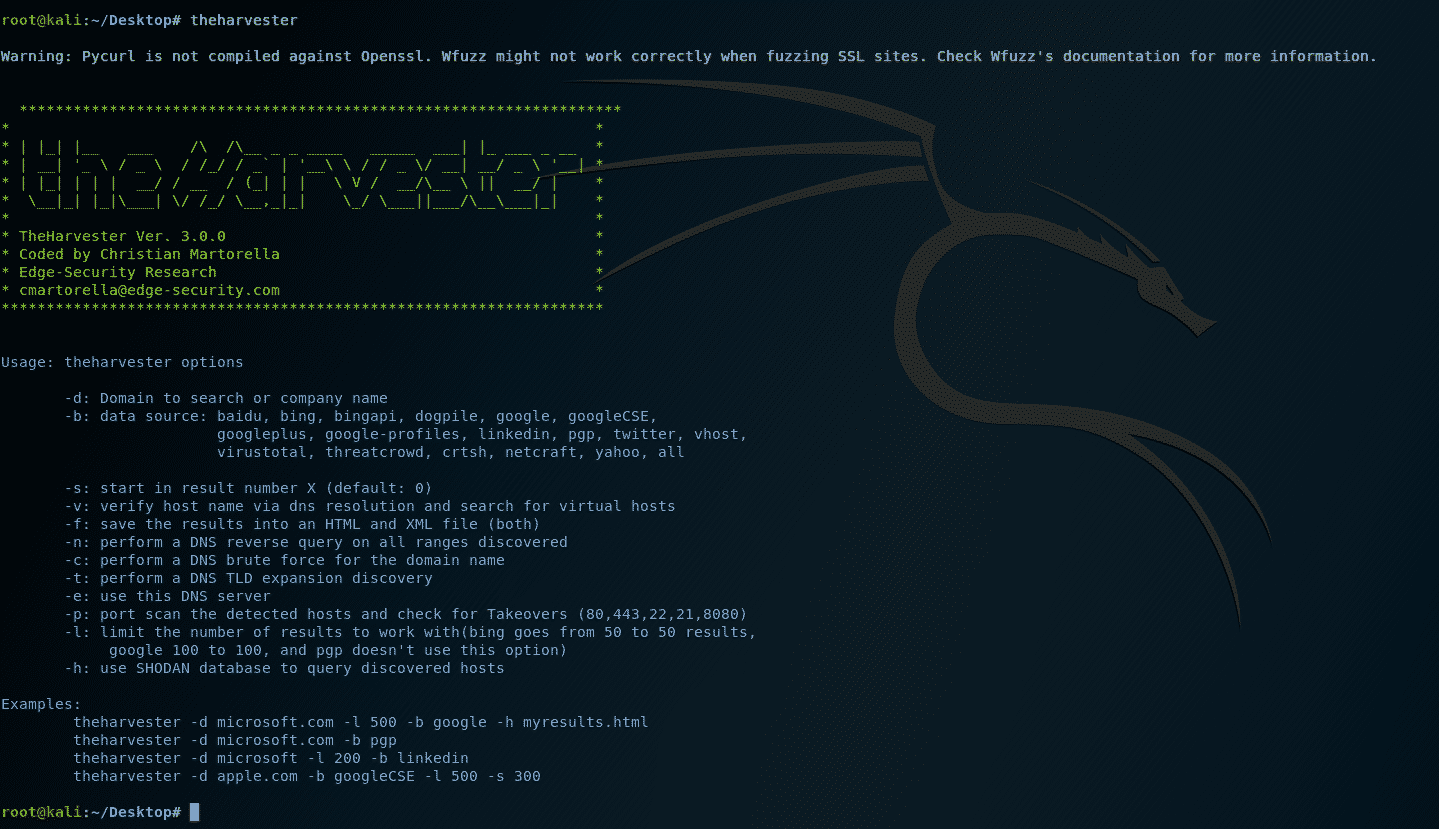
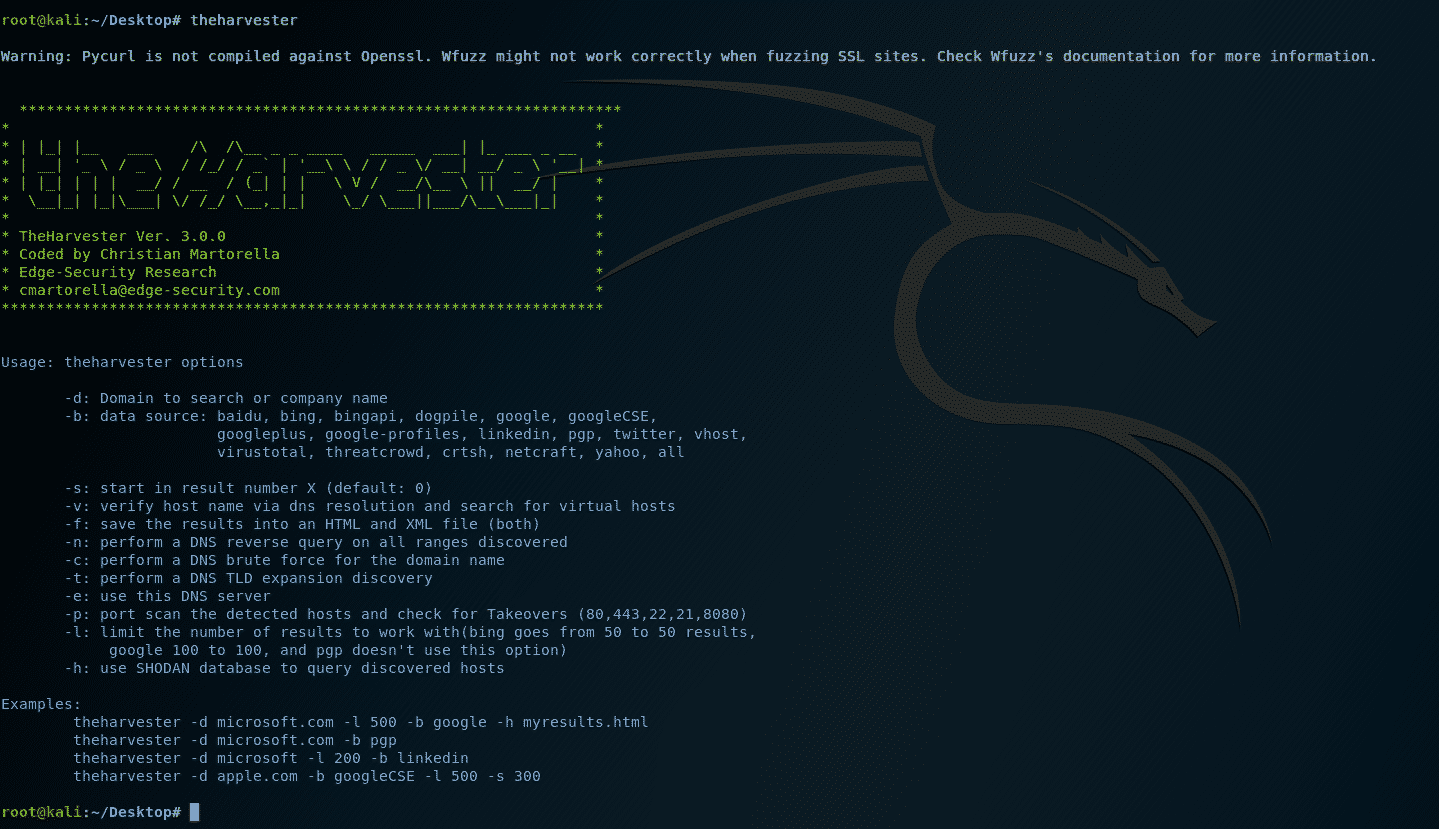
How to use theHarvester
How to use theHarvester What is theHarvester? theHarvester is an open-source intelligence (OSINT) tool designed to collect information such as email addresses, subdomains, IP addresses, and URLs from various public sources. It’s commonly used in the reconnaissance phase of penetration testing to map an organization’s external footprint. Why use theHarvester? Utilizing theHarvester enables security professionals to efficiently gather critical data …
Read More

How to Setup and Use Recon-ng
How to Setup and Use Recon-ng Setting up Recon-ng to install recon-ng you must have Python 3.6 or higher installed on your system, Please follow the instructions below to assist you in how to setup and use Recon-ng on your operating system. What is Recon-ng What is Recon-ng? Recon-ng is a web reconnaissance tool that automates information gathering to aid …
Read More
How to use BeEF
How to use BeEF BeEF (Browser Exploitation Framework) is a powerful penetration testing tool that focuses on exploiting web browsers. It is particularly useful for assessing the security of browser-based environments and understanding the risks posed by browser vulnerabilities. Here is a quick overview to help students understand how to use BeEF: What is BeEF? Purpose: BeEF is designed to …
Read More

How to Anonymously File Share
How to Anonymously File Share 📁 Anonymous File Sharing | How to Use Magic-Wormhole for Fast & Secure Transfers November 13, 2024 Looking for a way to send files quickly and anonymously without sharing your IP or username? Magic-Wormhole lets you securely transfer files between devices using a unique, one-time code. Here’s how you can get started! 🛠 Steps to Share Files Anonymously with Magic-Wormhole: Step 1: …
Read More

Kali Linux Basics: Cheat Sheet for Beginners
- Cracking & Hacking
-
cc cleaner, clear logs, clear tracks after hacking, cracking & Hacking, kali linux, kali linux cheat sheet, log cleaner, penetration testing, remove logs, shred clearing tracks, timestomp
- November 13, 2024
💻Kali Linux Basics: Cheat Sheet for Beginners November 05, 2024 Table of Contents 🧭 Navigation & Directory Management 📝 File Operations 🔍 Search for Files and Text 📦 Package Management with APT 🔒 Permissions and Ownership 📊 System Monitoring 🌐 Network Essentials 💾 File Compression and Archiving 🔧 Process Management ⏰ Scheduling with Cron 🔑 SSH & Remote Access 🧭 Navigation …
Read More

Cyber Security Tools
⋆.🌼 Cyber Security Tools❣ 🌼.⋆ Open Data Playground Shodan Images Link Expander – Grabify IP Logger & URL Shortener cyberguideme/Tools: Cyber Security Tools payloadbox/sql-injection-payload-list: 🎯 SQL Injection Payload List Z4KKD/CIS261ProjectPhase3 CTFd/CTFd: CTFs as you need them ctf-writeups/banana-boy.md at master · VulnHub/ctf-writeups sbilly/awesome-security: A collection of awesome security resources hmaverickadams/TCM-Security-Sample-Pentest-Report: Sample pentest report provided by TCM Security DvorakDwarf/Infinite-Storage-Glitch: ISG lets you …
Read More

Can You Get Shodan Premium Membership for Free?
- Cracking & Hacking
-
Academic Affiliation, Academic Email, Academic Email Verification, Academic Resources, Can You Get Shodan Premium Membership for Free, cybersecurity, Cybersecurity Education, Cybersecurity Tools, Free Shodan Premium, IP Monitoring, Shodan Academic Membership, Shodan Academic Upgrade, Shodan Access, Shodan Features, Shodan Premium, Shodan Premium Benefits, Shodan Tutorial, Troubleshooting Shodan Upgrade., Vulnerability Scanning
- December 14, 2023
Can You Get Shodan Premium Membership for Free? In the dynamic world of cybersecurity, Shodan Premium is a valuable resource for professionals and enthusiasts alike. But what if we told you that there’s a way to access Shodan Premium for free? In this guide, we’ll explore the possibility of obtaining Shodan Premium without opening your wallet. With an academic email …
Read More

What Should a UI/UX Designer Know?
What Should a UI/UX Designer Know? Exploring the Essentials of UI/UX Design In the dynamic and user-centric world of UI/UX design, it’s crucial to stay informed about the latest trends, tools, and best practices. Whether you’re a seasoned designer or just starting in the field, knowing what you should focus on can greatly enhance your skills. Let’s dive into what …
Read More
Top SEO strategies that work Fast
Top SEO strategies that work Fast Ranking #1 in Google SEO Strategies for Achieving the Number 1 Ranking in Search Engines SEO Strategies That Work Fast SEO Strategies That Work FastIn today’s competitive digital landscape, securing the top spot on Google’s search results is a coveted achievement. To achieve this, you need a combination of effective SEO strategies and a …
Read More