How to Secure Your Website
- Cyber Security
-
Cloudflare setup, CSRF protection, cybersecurity checklist, free website security, html site protection, HTTPS, malware removal, secure configuration, secure hosting, shopify security, SQL injection fix, SSL, WAF, web hardening, website protection, website security, wordpress security, XSS prevention
- October 23, 2025
How to Secure Your Website Three Methods: WordPress – Shopify – Self-hosted HTML site ( Top 25 list ) Securing your website doesn’t have to cost a dime — it just requires the right steps and consistency. Whether you’re running a WordPress blog, a Shopify storefront, or a self-hosted HTML site, there are free, proven methods to defend against hackers, …
Read More
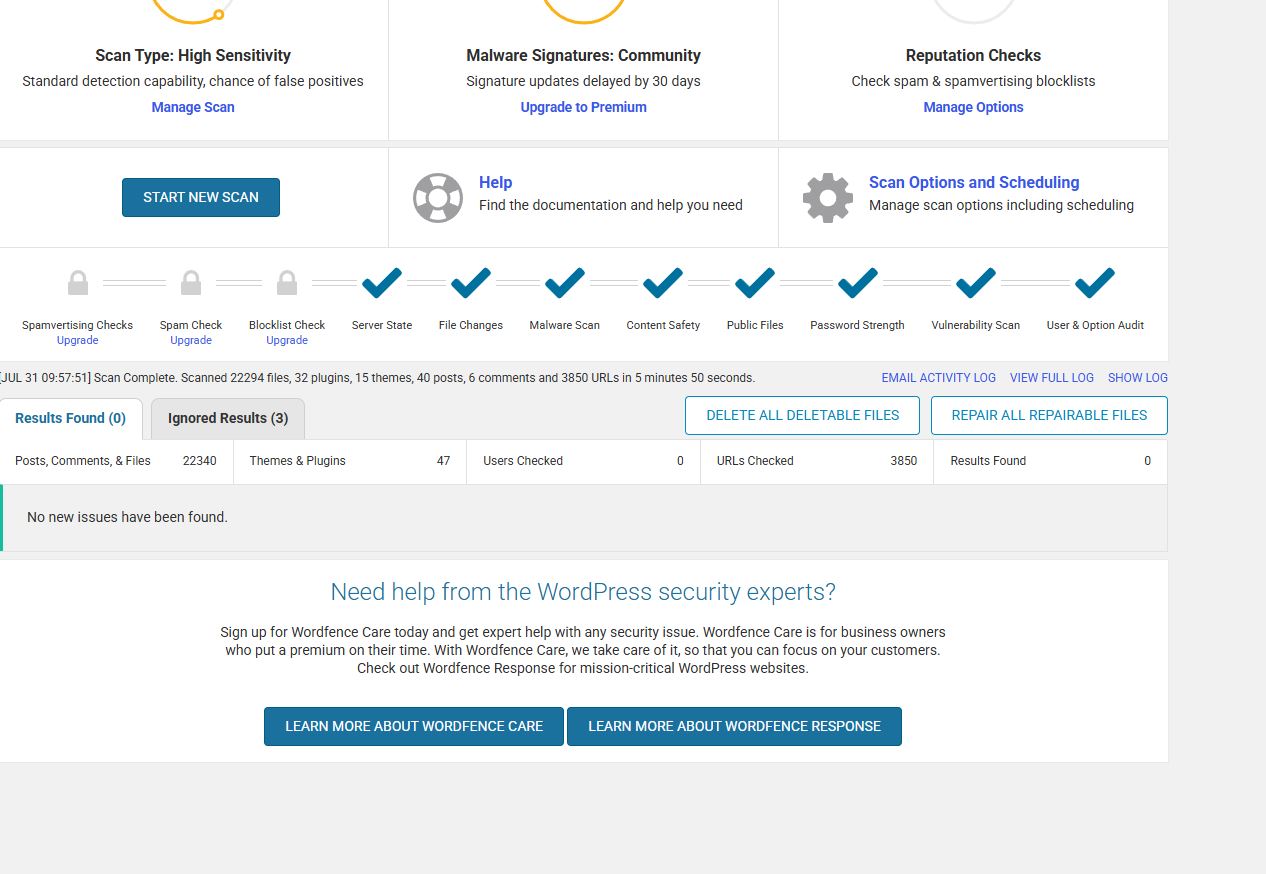
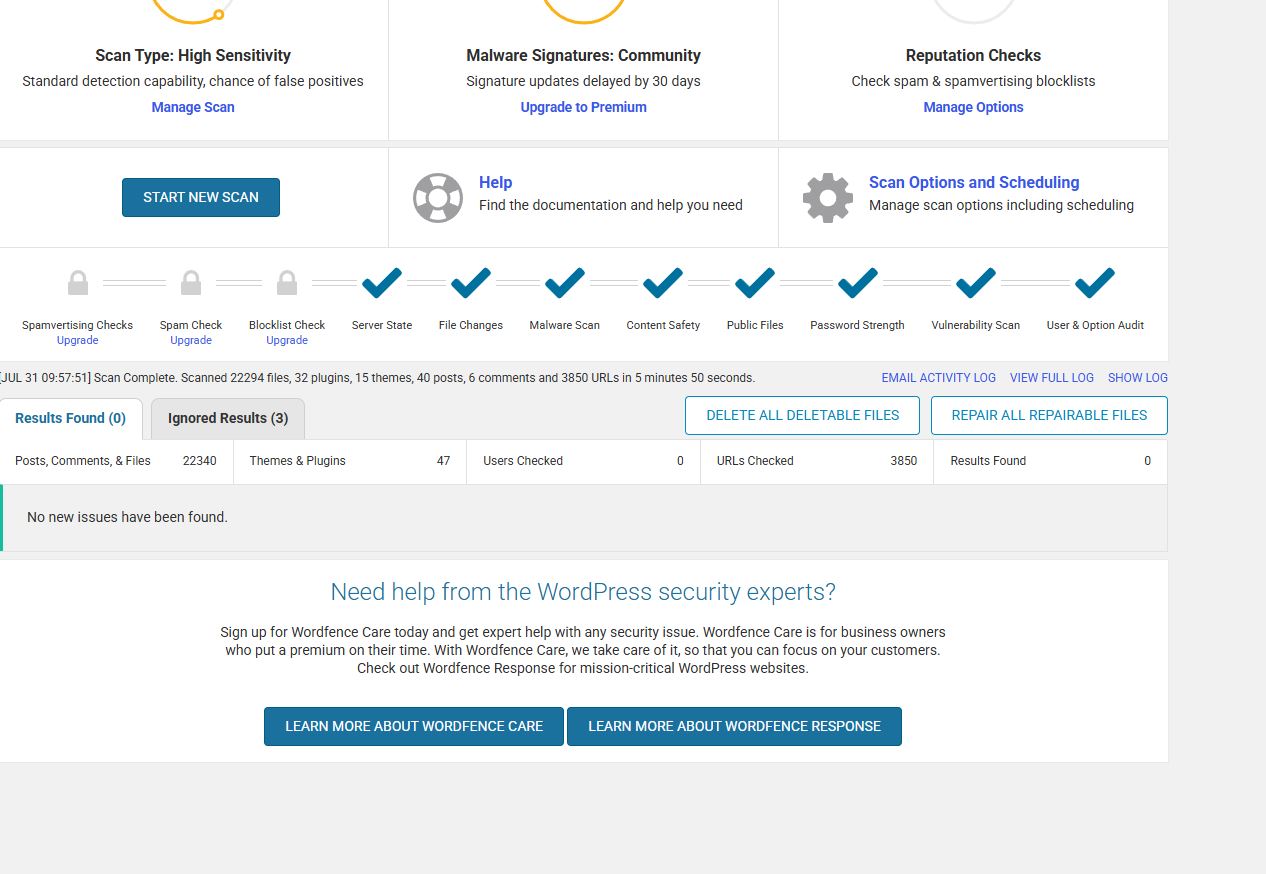
How I Secured My WordPress Blog – A Real-World Cybersecurity Walkthrough
- Cyber Security
-
blog hardening, cybersecurity, ethical hacking, free security tools, kali linux, secure blog setup, website security, website vulnerability, Wordfence, WordPress
- July 31, 2025
How I Secured My WordPress Blog – A Real-World Cybersecurity Walkthrough This post documents how I secured my WordPress blog using free tools, plugins, and configuration changes. The process simulates real-world website hardening and vulnerability management, which is useful for anyone studying cybersecurity, running a blog, or wanting to understand how attackers target insecure setups. Step 1: Scan Your Site …
Read More
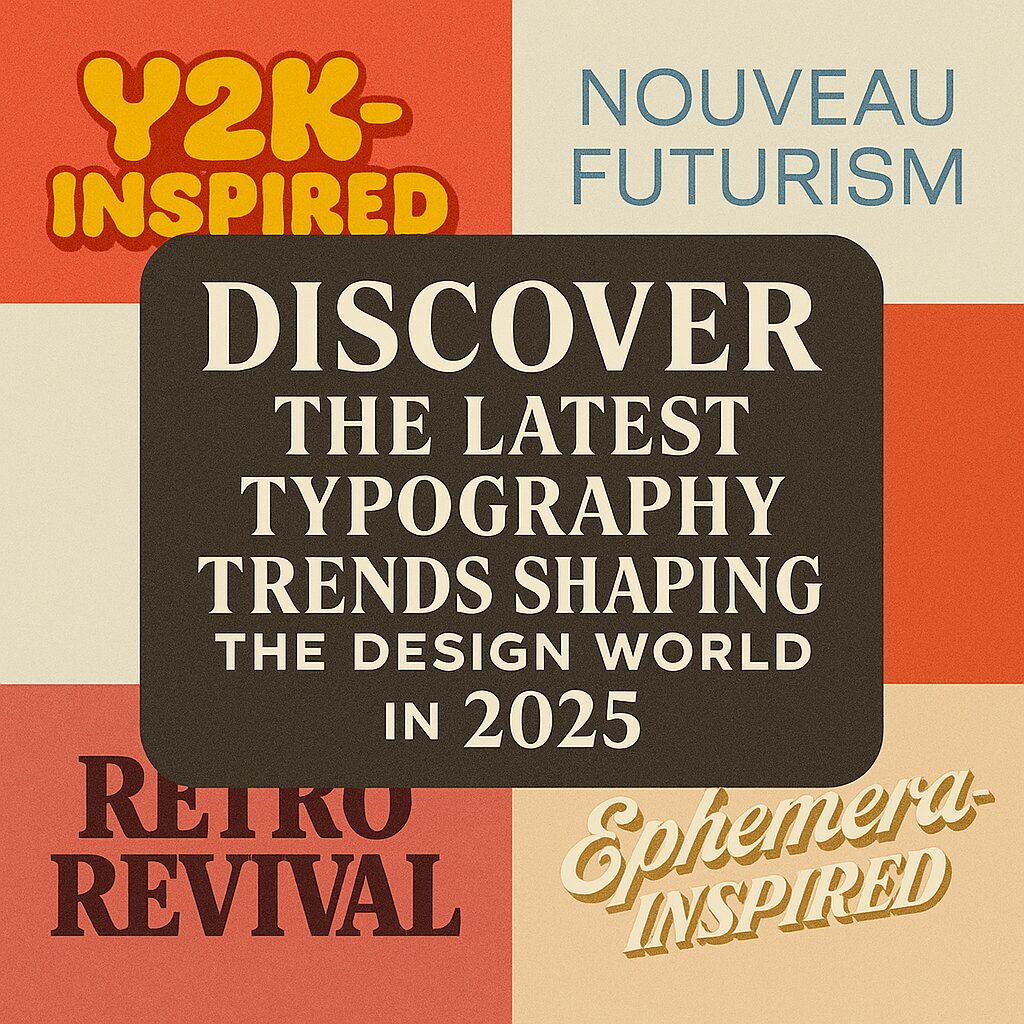
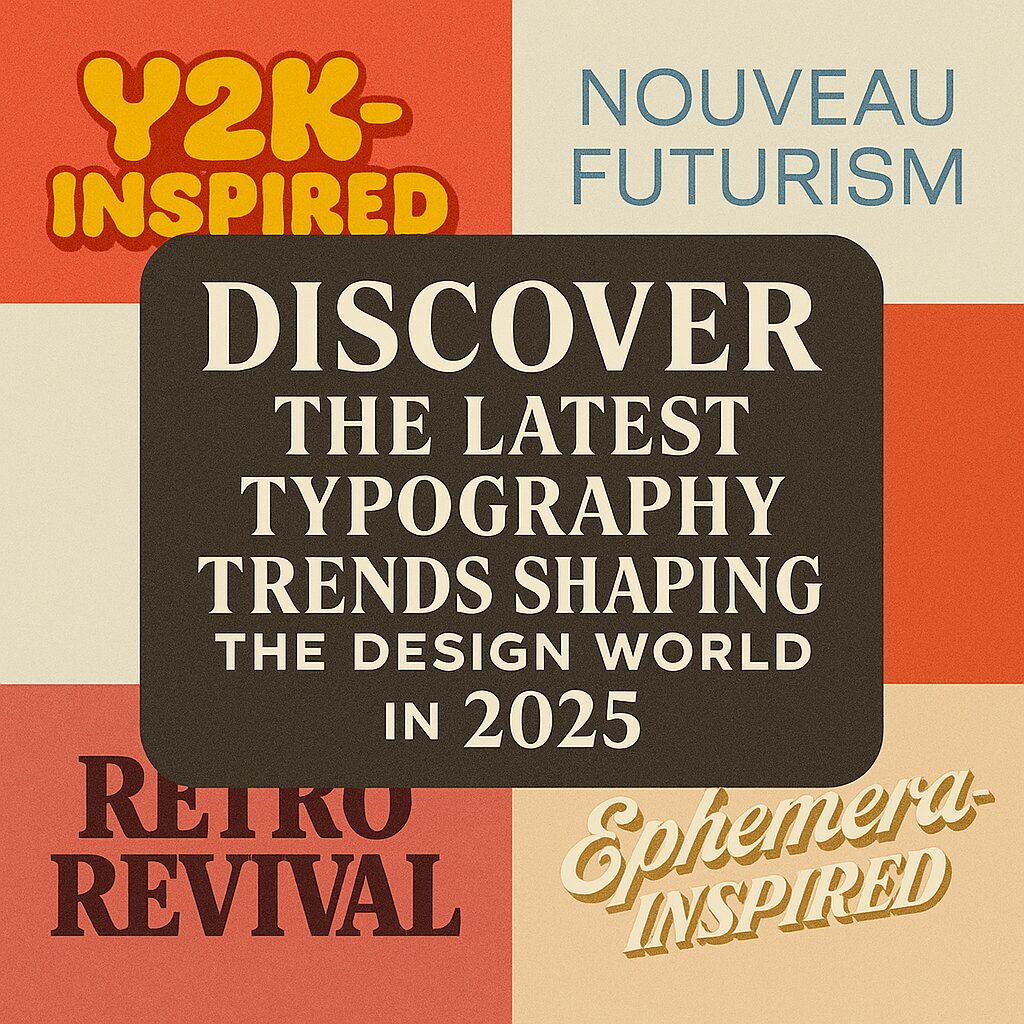
Discover the latest typography trends shaping the design world in 2025
- Graphic Designer Tips
-
AI typography, AI-generated fonts, branding design, design trends 2025, digital typography, ephemera typography, graphic design trends, modern typography, nouveau futurism, retro fonts, typography trends, vintage-inspired fonts, Y2K typography
- May 31, 2025
Discover the latest typography trends shaping the design world in 2025 Discover the Latest Typography Trends Shaping the Design World in 2025 Typography is evolving at a rapid pace, shaping how brands communicate and how designers create compelling visuals. In 2025, typography trends are being influenced by nostalgia, technology, and a renewed focus on storytelling. Whether you’re a graphic designer, …
Read More
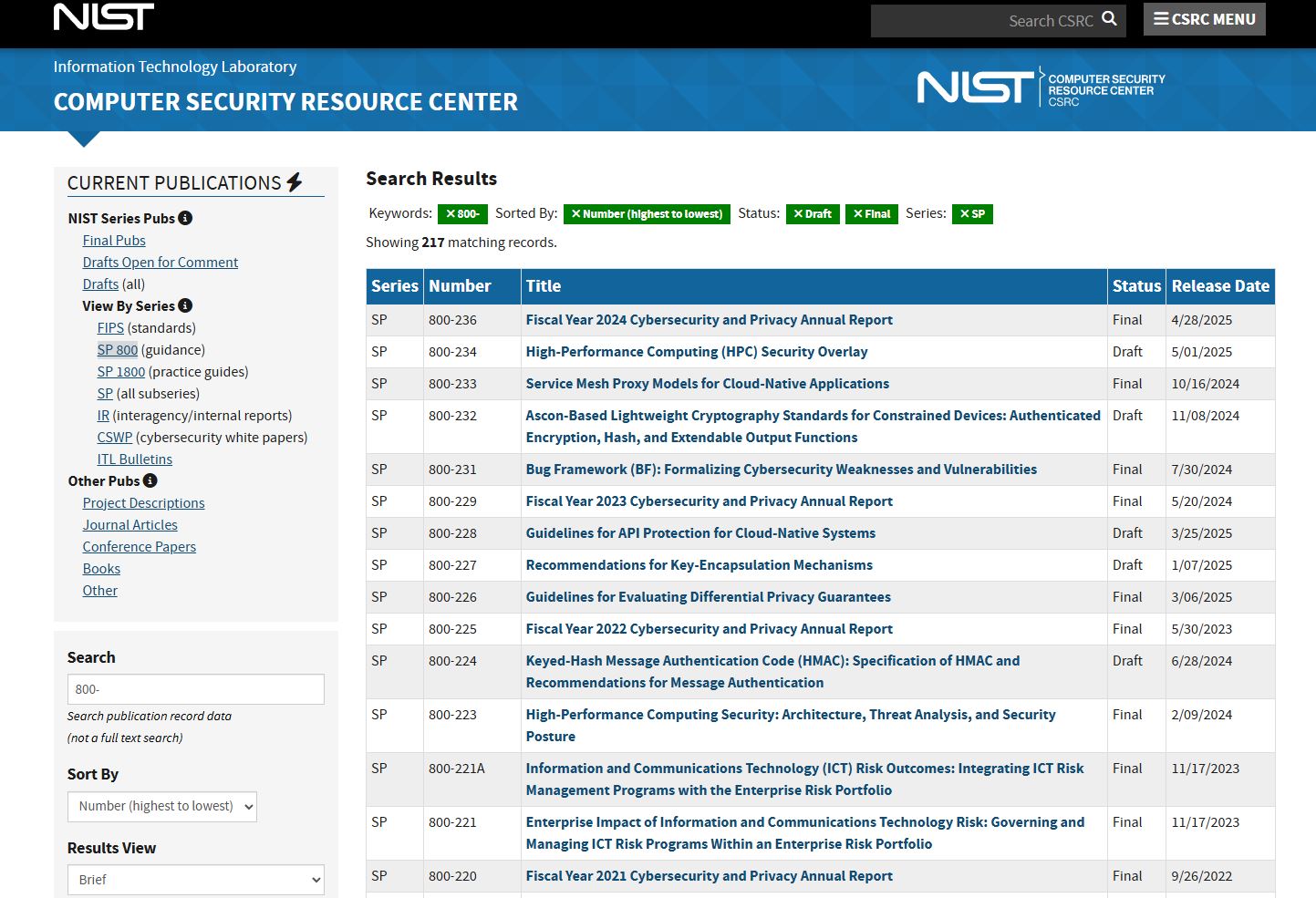
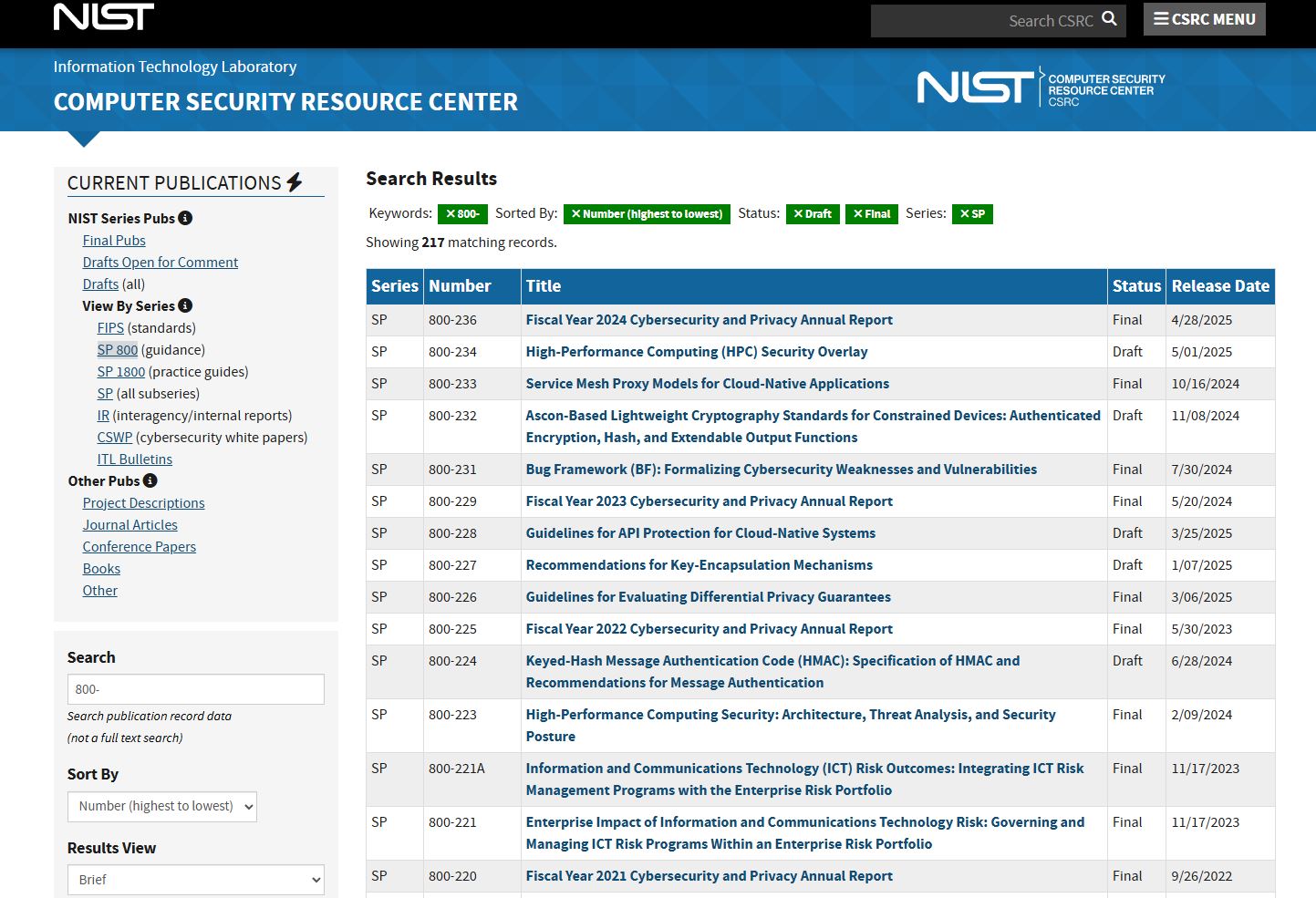
Download These Free NIST Cybersecurity Docs to Boost Your CISSP Prep
- Cyber Security
-
CISSP, cybersecurity, cybersecurity framework, federal security standards, Free NIST Cybersecurity Docs, free NIST PDF, How to download NIST guidelines, incident response, NIST, NIST list, NIST PDF Download, NIST research, NIST SP 800-53, risk management, security certification, SP 800 series
- May 31, 2025
Download These Free NIST Cybersecurity Docs to Boost Your CISSP Prep If you’re studying for the CISSP or working in cybersecurity, you need to know about NIST. The National Institute of Standards and Technology publishes free, authoritative guidelines that shape the backbone of modern cybersecurity. These documents—like SP 800-53 and the Cybersecurity Framework (CSF)—are not just useful; they’re foundational. In …
Read More

FREE A+ Certification Online Flash Cards
- Cerification Flash Cards
-
A+ Certification, A+ exam, certification study guide, CompTIA A+, computer certification, exam prep, free flashcards, IT certification, online flashcards, study flashcards
- February 22, 2025
FREE A+ Certification Online Flash Cards hello Friends I have created 70 + Questions and answers in an online Flash card Form for you to study for your A+ Certification exam. Directions simply click on the card to reveal the answer and use the back and forward keys to navigate through the questions. Hashtags: #APlusCertification, #CompTIA, #Flashcards, #ExamPrep, …
Read More

The Impact of AI on Modern Graphic Design
The Impact of AI on Modern Graphic Design Artificial Intelligence (AI) has rapidly become a cornerstone in various industries, and graphic design is no exception. The integration of AI into design processes is revolutionizing the way designers work, offering tools that enhance creativity, efficiency, and innovation. AI-Powered Design Tools Modern AI-powered design tools are capable of automating routine tasks, allowing …
Read More
The Evolution of Typography in Digital Media
The Evolution of Typography in Digital Media The Evolution of Typography in Digital Media Typography has been an essential element of design for centuries, evolving with technological advancements and artistic movements. In digital media, typography plays a crucial role in branding, user experience, and visual storytelling. The transformation of typography in the digital space has been driven by innovations in …
Read More

The Rise of AI-Powered Graphic Design Tools
The Rise of AI-Powered Graphic Design Tools The Rise of AI-Powered Graphic Design Tools The graphic design industry is undergoing a major transformation, thanks to the rapid advancement of artificial intelligence (AI). AI-powered tools are revolutionizing the way designers work, making the process faster, more efficient, and highly intuitive. From automated design generation to intelligent color and font suggestions, AI …
Read More

The Psychology of Colors in Branding and Marketing
The Psychology of Colors in Branding and Marketing The Psychology of Colors in Branding and Marketing Color plays a crucial role in branding and marketing. It’s not just about aesthetics; colors evoke emotions, shape perceptions, and influence consumer behavior. The right color choices can make a brand instantly recognizable and trigger subconscious associations that drive purchasing decisions. How Colors Impact …
Read More

Lets hack your home network
- Cracking & Hacking
-
Android ADB exploit, brute force hacking, cybersecurity, ethical hacking, ethical hacking tutorial, find devices on network, hacking tools, home network security, MITM attack, network discovery, nmap scanning, open ports, penetration testing, router security, Windows SMB exploit
- February 12, 2025
Lets hack your home network Step 1: Network Discovery (Finding Devices) 1. Identify Your Network Subnet First, find your network’s IP range. Open a terminal and run: bash CopyEdit ip a | grep inet or bash CopyEdit ifconfig Look for something like 192.168.1.x or 10.0.0.x. The subnet is likely 192.168.1.0/24. 2. Scan the Network for Devices Use nmap to find …
Read More